Attacker Value
Very High
2
CVE-2021-38840
2
CVE ID
AttackerKB requires a CVE ID in order to pull vulnerability data and references from the CVE list and the National Vulnerability Database. If available, please supply below:
Add References:
CVE-2021-38840
(Last updated November 28, 2024) ▾
MITRE ATT&CK
Log in to add MITRE ATT&CK tag
Add MITRE ATT&CK tactics and techniques that apply to this CVE.
Execution
Techniques
Validation
Validated
Validated
MITRE ATT&CK
Select the MITRE ATT&CK Tactics that apply to this CVE
Collection
Select any Techniques used:
Command and Control
Select any Techniques used:
Credential Access
Select any Techniques used:
Defense Evasion
Select any Techniques used:
Discovery
Select any Techniques used:
Execution
Select any Techniques used:
Exfiltration
Select any Techniques used:
Impact
Select any Techniques used:
Initial Access
Select any Techniques used:
Lateral Movement
Select any Techniques used:
Persistence
Select any Techniques used:
Privilege Escalation
Select any Techniques used:
Topic Tags
Select the tags that apply to this CVE (Assessment added tags are disabled and cannot be removed)
What makes this of high-value to an attacker?
What makes this of low-value to an attacker?
Description
SQL Injection can occur in Simple Water Refilling Station Management System 1.0 via the water_refilling/classes/Login.php username parameter.
Add Assessment
1
Ratings
-
Attacker ValueVery High
-
ExploitabilityVery High
Technical Analysis
CVE-2021-38840
Vendor
Software
Description:
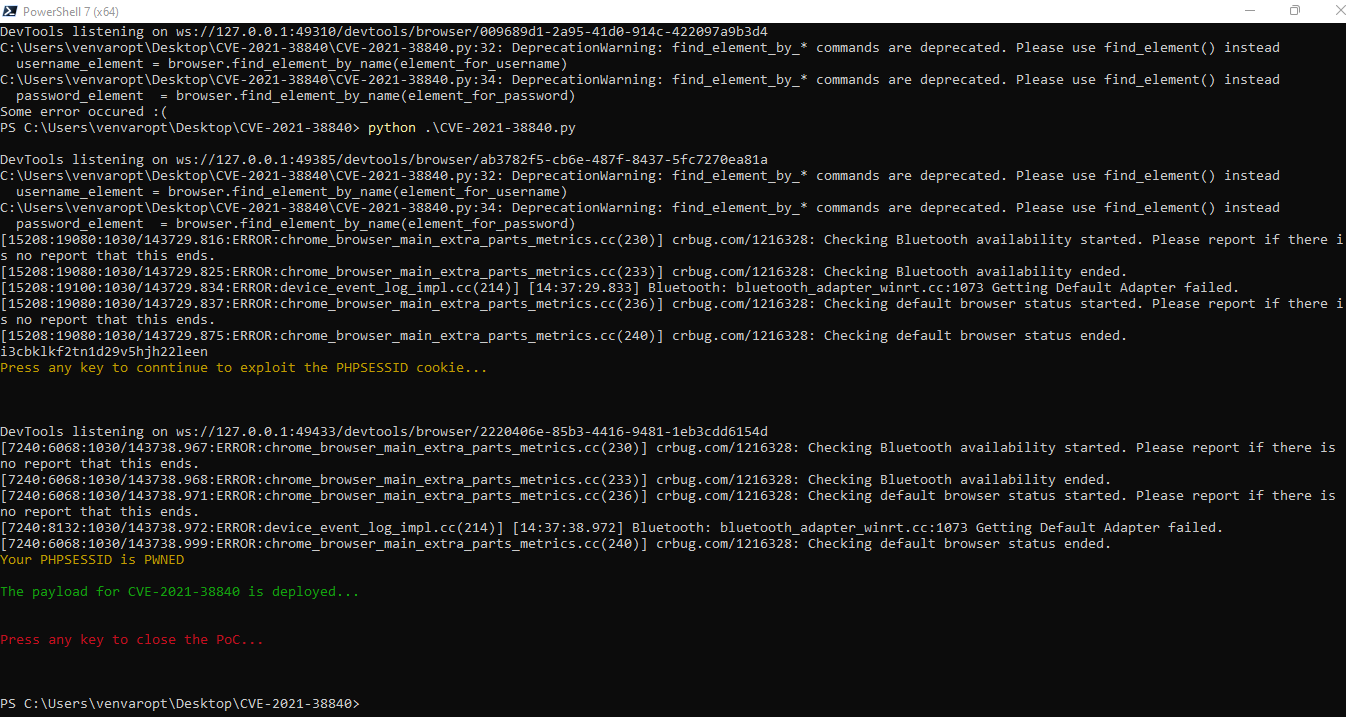
The Water Refilling System – PHP (by: oretnom23 ) v1.0 is vulnerable to remote SQL-Injection-Bypass-Authentication + XSS-Stored Hijacking PHPSESSID
- m0re info: https://portswigger.net/support/using-sql-injection-to-bypass-authentication.
The parameter (username) from the login form is not protected correctly and there is no security and escaping from malicious payloads.
When the user will sending a malicious query or malicious payload to the MySQL server he can bypass the login credentials and take control of the administer account.
- XSS – Stored PHPSESSID Vulnerable
- The vulnerable XSS app: is “maintenance”, parameters: “name” After the successful SQL injection, the malicious user can be storing an XSS payload whit who can take the
active PHPSESSID session.
- remote PHPSESSID – Injection
- After the successful XSS attack the malicious user can take control of the administrative account of the system from everywhere
by using the PHPSESSID, and then he can make a lot of bad things!
CONCLUSION: This vendor must STOP creating all these broken projects and vulnerable software programs, probably he is not a developer!
BR
- [+] @nu11secur1ty System Administrator – Infrastructure and Penetration Testing Engineer
Reproduce:
Proof:
BR nu11secur1ty
Would you also like to delete your Exploited in the Wild Report?
Delete Assessment Only Delete Assessment and Exploited in the Wild ReportCVSS V3 Severity and Metrics
Data provided by the National Vulnerability Database (NVD)
Base Score:
9.8 Critical
Impact Score:
5.9
Exploitability Score:
3.9
Attack Vector (AV):
Network
Attack Complexity (AC):
Low
Privileges Required (PR):
None
User Interaction (UI):
None
Scope (S):
Unchanged
Confidentiality (C):
High
Integrity (I):
High
Availability (A):
High
General Information
Offensive Application
Unknown
Utility Class
Unknown
Ports
Unknown
OS
Unknown
Vulnerable Versions
n/a
Prerequisites
Unknown
Discovered By
Unknown
PoC Author
Unknown
Metasploit Module
Unknown
Reporter
Unknown
References
Miscellaneous
Additional Info
Authenticated
Unknown
Exploitable
Unknown
Reliability
Unknown
Stability
Unknown
Available Mitigations
Unknown
Shelf Life
Unknown
Userbase/Installbase
Unknown
Patch Effectiveness
Unknown
Rapid7
Technical Analysis
Report as Emergent Threat Response
Report as Zero-day Exploit
Report as Exploited in the Wild
CVE ID
AttackerKB requires a CVE ID in order to pull vulnerability data and references from the CVE list and the National Vulnerability Database. If available, please supply below:
